Top 10 Enterprise Cybersecurity Threats for 2024
The world of cybersecurity is ever-evolving, with new cybersecurity threats constantly surfacing. Organizations need to protect sensitive information from cyber threats. We’re likely to see security threats become more sophisticated and expensive: experts predict that the global costs of cybercrime will reach $10.5 trillion by 2025.
Let’s explore enterprise cybersecurity and review the top 10 enterprise cybersecurity threats.
Are Budget Constraints Exposing Companies to Cyber Threats?
A new study by Neustar found that only 4 in 5 executives believe their C-suite and board understand the existing cybersecurity threat levels, but more than 2/3 agree that budget constraints limit their ability to respond to these risks. Despite the rising sophistication and number of cyber threats, many companies are struggling to allocate sufficient funds to protect against them. The shift to hybrid work has also made it more challenging to secure the workplace from outside threats. As a result, companies are increasingly turning to managed service providers for cloud-based security solutions.
What is Enterprise Cybersecurity?
Enterprise cybersecurity includes everything that protects a company’s data, resources, and users/customers from cyberattacks. It includes protecting on-premise data, cloud-based data, and the many endpoints through which cyberattacks can come. Enterprise cybersecurity also analyzes data routes between devices, networks, and people and makes each element as secure as possible.
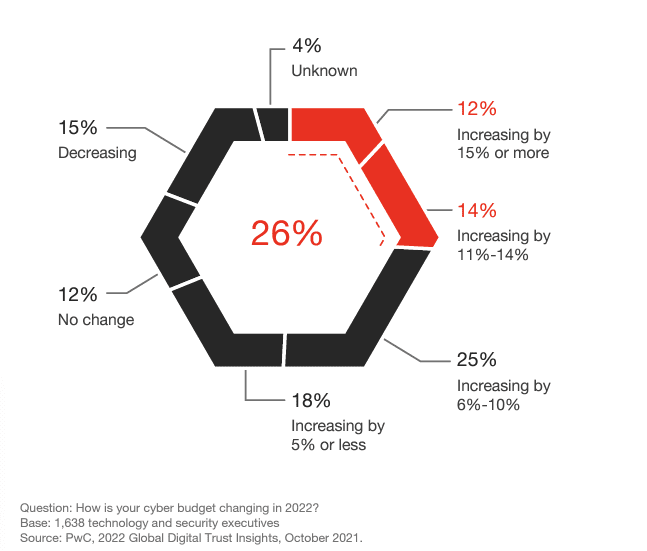
Sixty-nine percent of organizations planned to increase cybersecurity spending in 2022, driven by the business case of securing increasingly complex digital infrastructures their businesses rely on.
10 Enterprise Cybersecurity Threats to Avoid in 2024
1. Social Engineering
Social engineering is one of the most dangerous hacking techniques cybercriminals use. Instead of prying on technical vulnerabilities, it relies on human error – which is far easier to trick than breaching a security system. According to Verizon’s Data Breach Investigations report, 85% of all data breaches involve human interaction.Hackers will use social media or other information that people leave about themselves on the internet and lure people to expose data, provide access to restricted systems, or introduce malware into their enterprise. “Catfishing” is a form of social engineering.
2. Third-Party Exposure
Cybercriminals can beat security systems by hacking less-protected networks belonging to third parties with privileged access to the hacker’s primary target. In 2024, third-party breaches will become an even more serious threat as companies increasingly hire independent contractors to complete work once handled by full-time employees. The cybersecurity firm CyberArk reports that 96% of organizations grant external parties access to critical systems, providing a potentially unprotected access route to their data to be exploited.
3. Configuration Mistakes
Even the most robust security systems may contain at least one error in how the software is installed and set up. In 268 trials conducted by cybersecurity software company Rapid7, 80% of external penetration tests encountered an exploitable misconfiguration. In tests where the attacker had internal system access (i.e., trials mimicking access via a third party or infiltration of a physical office), the amount of exploitable configuration errors rose to 96%.
4. Malware
Malware is malicious software, including viruses and worms, injected into networks and systems to cause disruption. Malware can extract confidential information, deny service and gain access to systems. IT departments use antivirus software and firewalls to monitor and intercept malware before it gains access to networks and systems. Still, bad actors continue to evolve their malware to elude these defenses. That makes maintaining current updates to security software and firewalls essential.
5. Ransomware
Ransomware is a type of malware whose specific purpose is to blocks access to a system and/or threaten to publish proprietary information. Ransomware hackers demand that their victims’ companies pay them cash ransoms to unlock systems or return information. According to research conducted by Check Point, in the last decade, ransomware has grown to a $20B a year industry, and while progressive solutions have made it more difficult for ransom actors to succeed, hoping to stop ransomware at execution is not a viable long-term strategy.
6. Phishing
If you have ever received a suspicious email, or even one that appears to be legitimate and from a trusted party but isn’t, you have fallen prey to phishing. Phishing is a serious problem for companies, as unsuspecting employees often open fake emails that unleash viruses or malware. Phishing is one of the most common delivery methods for ransomware. Although phishing is sometimes inevitable, employee training on recognizing phony emails, reporting them, and never opening them can help mitigate issues.
7. The Internet of things (IoT)
The Internet of things (IoT) describes physical objects (or groups of such objects) with sensors, processing ability, software and other technologies that connect and exchange data with other devices and systems over the Internet or other communications networks. In 2020, 61% of companies were using IoT, and this percentage is increasing. With the growth of IoT, security risks also grow, particularly with the creation of 5G telecommunications. Many IoT vendors are notorious for implementing little to no security. However, Enterprises can improve this through stronger vetting of IoT vendors upfront in the RFP process for security and resetting IoT security defaults on devices to adhere to stricter measures.
8. DDoS attacks
Distributed Denial of Service (DDoS) attacks are a common and increasingly sophisticated threat that can cause significant disruption to an enterprise’s online presence. DDoS attacks work by overwhelming a website or web-based service with a flood of traffic from multiple sources, making it difficult or impossible for legitimate users to access it. These attacks can be launched using various methods, such as botnets, amplification attacks, and application-layer attacks.
One of the main challenges of DDoS attacks is that they can originate from anywhere in the world, making it difficult to trace the attackers. Additionally, DDoS attacks are becoming more sophisticated, with attackers using techniques such as multi-vector attacks, which use multiple methods to attack a single target simultaneously, making it even more difficult to defend against.
To protect against DDoS attacks, it’s important to have a robust network infrastructure in place, including firewalls, intrusion prevention systems, and load balancers. Additionally, it’s crucial to have a plan in place to respond to a DDoS attack, including identifying the attack early, activating incident response protocols, and engaging a DDoS mitigation service to help filter out the malicious traffic.
Another important step is to test and simulate DDoS attacks regularly to ensure that your organization is prepared to respond. This can be done by using DDoS testing and simulation tools, which can help to identify any vulnerabilities in your network and ensure that your incident response protocols are effective.
In conclusion, DDoS attacks are a serious threat that can cause significant disruption to an enterprise’s online presence. It’s important to have a robust network infrastructure in place and to have a plan in place to respond to a DDoS attack, including identifying the attack early, activating incident response protocols, and engaging a DDoS mitigation service to help filter out the malicious traffic. Regular testing and simulation can also help to identify any vulnerabilities in your network and ensure that your incident response protocols are effective.
9. Poor Data Management
Data management is not just keeping storage and organization in place. Conversely, data created by consumers double every four years, but more than half of that new data is never used or analyzed. Piles of surplus data lead to confusion, leaving data vulnerable to cyber-attacks. Breaches caused by data handling mistakes can be just as costly as higher-tech cybersecurity attacks.
10. Cloud Vulnerabilities
Although cloud technology is advancing, it is also ironically becoming less secure over time:
IBM reports that cloud vulnerabilities have increased by 150% in the last five years. According to Gartner, cloud security is currently the fastest-growing cybersecurity market segment, with a 41% increase from $595 million in 2020 to $841 million in 2021.
Avoid Cybersecurity Threats with a Solid Enterprise Cybersecurity Plan
Although the long list of looming cybersecurity threats may seem overwhelming, with the right cybersecurity infrastructure, your enterprise can avoid these threats. Make the right choice for your enterprise cybersecurity solutions with Olive. If you have had enough of constantly comparing cybersecurity solutions and vendors and endlessly searching reviews and products, Olive can help you.
How to Choose the Best Cybersecurity Solutions for Your Enterprise
Check Out Olive’s Cybersecurity Project and Requirements Templates
With Olive, getting started on your cyber security project is easy. You can choose from a variety of pre-built templates or create your own custom requirements. No matter the complexity of your project, Olive has the tools to help you kick off your requirements-gathering process. To get started, simply select one of the pre-built cyber security tech stack project templates and begin customizing it to fit your specific needs.
Invite Security Software Vendors to Respond to Requirements
Olive does not charge vendors. We facilitate vendor-neutral decisions based on exactly what you need, not what vendors are selling or subjective reviews. Olive allows you to invite vendors to respond to requirements, without revealing the identity of your client or business.
Compare Vendors to Criteria in Olive
Gartner, G2 Crowd, and Capterra can give you a good overview of the top-rated vendors on the market, but shortcutting the process and only reviewing a few solutions in the space is fraught with risk and bias. Choosing the wrong solution will cost you in the long run. Olive helps you find the right solution for your needs with a thorough, collaborative evaluation.
Find your Organization’s Best-fit Security Software Tech Stack
Choosing the best cloud ERP software may seem daunting, but it doesn’t have to be. Olive helps you find the best-fit security software to fit your business needs.