Enterprise Shadow IT, What It is and How to Prevent It
In this article we delve into the world of Shadow IT, its risks and perceived benefits, and most importantly, how to prevent it. Despite its prevalence in many enterprises, Shadow IT often remains “the elephant in the room”, many enterprises are reluctant to discuss it due to its perceived benefits or a reluctance to highlight problems and weaknesses in IT technology infrastructure. Neglecting these issues may result in more significant problems in the future. Therefore, it’s crucial for companies to take a proactive approach in addressing Shadow IT.
With the right measures in place, it is possible to effectively tackle the issue of Shadow IT and safeguard your organization from its potential pitfalls.
What is Shadow IT?
Shadow IT is the use of information technology systems, devices, software, applications, and services without explicit IT department approval. With the adoption of cloud-based applications and services in recent years, it has grown at an exponential rate. While shadow IT can boost employee productivity and drive innovation, it also poses serious security risks to your organization due to data leaks, potential compliance violations, and other issues.
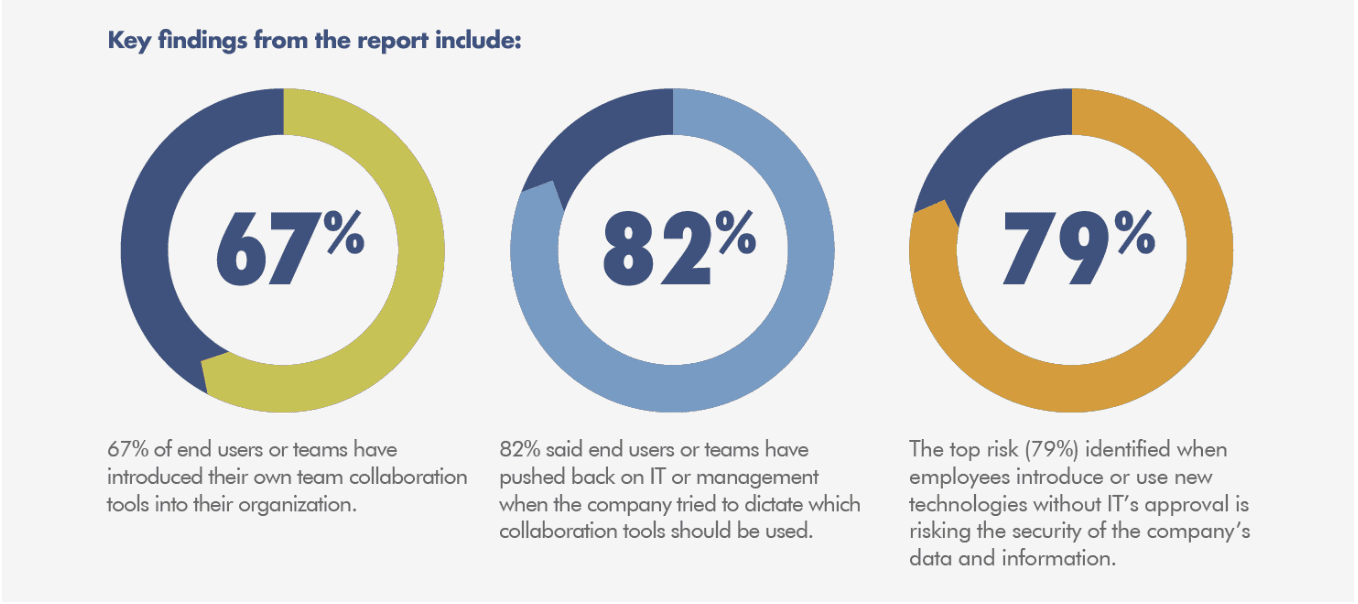
In a recent survey, collaboration tools bubbled up as a risky category, with over two-thirds of teams saying that they’ve implemented their own deployments without coordinating with IT. 82 percent or respondents have pushed back against IT’s attempts to implement a vetting process for collaboration tools.
Why Shadow IT Occurs
One of the most common reasons employees engage in shadow IT is to improve their productivity. An employee may discover a better file-sharing application than the one that is officially permitted. When they start using it, the application may spread to other members of their department. The rapid expansion of cloud-based consumer applications has also increased the use of shadow IT. The days of packaged software are long gone; common applications like Slack and Dropbox are now available with the click of a button. And, as the term “Bring Your Own Device” (BYOD) suggests, shadow IT extends beyond work applications to employees’ personal devices such as smartphones or laptop computers.
Shadow IT Problems and Security Risks
Companies must not underestimate the level of risk posed by the use of unauthorized tools, applications, or devices, any of which can serve as an access point for a cybercriminal. As organizations face a dangerous threat landscape, it is critical to limit the risk posed by shadow IT. Shadow IT dangers include:
- Visibility and Control: Shadow IT, by definition, exists outside the scope of IT security, increasing the likelihood that vulnerabilities, misconfigurations, and policy violations will go undetected.
- Data Loss: Another issue with shadow IT is that data or other assets stored in personal accounts are inaccessible to others in the organization. If an employee resigns or is fired, they could still have access to the cloud assets, whereas the organization may lose access to those assets.
- Data Theft: While data loss is a major concern for businesses, data theft may pose an even greater risk. Every case of shadow IT increases the organization’s attack surface. Shadow IT assets are not protected by the organization’s cybersecurity solutions, such as endpoint detection and response (EDR), next-generation antivirus (NGAV), or threat intelligence services, because they are not visible to the IT or cybersecurity teams. Furthermore, shadow IT services are typically created with weak or default credentials or are misconfigured, all of which can be exploited by cybercriminals and used as a gateway into the organization’s larger corporate network.
- Cost: In many cases, employees turn to shadow IT to save money. However, long-term use of these services, or scaling them across the organization, may not be cost-effective. As per Gartner studies, shadow IT accounts for 30-40% of IT spending in large enterprises. Shadow IT also adds indirect costs, such as noncompliance fines and penalties, reputational damage in the case of a breach, or timely IT support if and when the service needs to be migrated or de-provisioned.

Source: What is Shadow IT? Necessity & Its Impact on Enterprise Security via Cloud Codes
Organizations can reduce risk by educating employees and implementing preventative measures to oversee unapproved applications.
Perceived Benefits of Shadow IT
Companies may not want to talk about Shadow IT because it highlights problems and weaknesses in their technology infrastructure. However, ignoring the issue can lead to bigger problems down the line, so it’s important for companies to address Shadow IT proactively. Despite its risks, shadow IT also has some perceived benefits, that often drive short term results, such as:
- Access to resources more quickly, which can improve employee efficiency and reduce potential bottlenecks
- Reduced costs by utilizing free or low-cost cloud-based services.
- Self-service of basic requests optimizes limited IT resources and frees up time, including staff
- Improved communication and collaboration via highly intuitive and user-friendly applications and platforms
- A better user experience by reducing time lags related to administration and bureaucracy
How to Avoid Shadow IT
If you’ve done the math and find that your Shadow IT risks outweigh the benefits, it’s time to strategize and figure out the best course of action. Let’s take a look at how to avoid Shadow IT from occurring. When it comes to cloud security, the need to balance innovation against security risks presents an existential challenge to your organization.
1. Stepping out of the shadow — get full visibility:
Shadow IT is becoming more common. It’s a remote employee using a free cloud tool to complete a one-time task, or it’s onboarding contractors and vendors because your roadmap’s demands are outpacing security procedures. Shadow IT is pervasive, but it is essentially invisible to IT. To enable secure digital transformation, your organization requires full visibility into sanctioned and unsanctioned cloud activity, app and vendor details, usage trends, and risk profiles. Olive prevents shadow IT by allowing for everyone to have visibility and provide input on vendor evaluations. Our user-friendly platform ensures all departments’ needs are considered by utilizing easy-to-build surveys and inviting key stakeholders to collaborate in the platform.
2. Analyze the Risk
Gaining visibility isn’t enough; the real value is in your ability to analyze risk factors and trends in your organization’s Shadow IT:
- Identify high-risk apps and app categories used within your organization.
- Obtain vendor compliance and certification status.
- Monitor the volume of requests to existing and new apps to manage app sprawl.
- Use a combination of vendor- and app-specific attributes to evaluate app risk levels.
- Utilize category-based reports, user data, and risk scores to improve optimization and enhance decision-making processes.
Olive reduces the risks of shadow IT by allowing everyone to see and provide feedback on vendor evaluations, enhancing the decision-making process. Our platform also aligns department needs by using simple surveys and inviting key stakeholders to collaborate on the platform.
3. Optimize and secure
While Shadow IT makes your employees’ jobs easier, it also makes it easier for attackers to do theirs. Malware infections are increased by using shadow IT resources such as cloud storage applications. Furthermore, insufficient security, combined with a lack of legal and regulatory compliance, makes sensitive data more susceptible to theft.
If you’re looking for ways to enhance your cloud malware detection but don’t know which software vendors to try, let Olive help you out. Olive helps teams collaborate on requirements management, vendor comparison, due diligence and solution selection. It’s more innovative, collaborative, and accurate than RFI/RFQ (asking questions or asking for information) or RFP (identifying use cases and asking for a proposal on how to solve them). Find the right vendor and improve your data protection when Shadow IT concerns are causing you to lose sleep.
Prevent Shadow IT with Olive
Olive prevents shadow IT by allowing for everyone to have visibility and provide input on vendor evaluations. No matter how large or small the purchase is, a tool like olive can ensure all departments’ needs are considered, including internal security needs.
With Olive, Your Enterprise can:
- Spend up to 66% less time on Enterprise Software Selection.
- Input all the transformation initiatives you plan to implement over the next 2-3 years with our project stages dashboard.
- Identify all current, future, and potential technology needs to build a deep understanding of overarching enterprise goals.
- Easily identify and prioritize detailed requirements to ensure that stakeholder needs are met, rather than asking solution providers what their solutions do or how their solutions could potentially meet a list of high-level use cases.
- Gain access to early vendor engagement, even before all needs may be specified, refined, or known. As key stakeholders and collaborators create and rank their most important requirements, vendors can be invited to begin their responses, even if all needs have not yet been identified or defined.