In today’s interconnected world, where cyber threats continue to evolve and grow in sophistication, enterprise cybersecurity has become paramount for businesses of all sizes. Staying ahead of the curve and adapting to emerging cybersecurity trends is crucial to safeguarding your company’s sensitive data, protecting customer trust, and ensuring uninterrupted business operations. In this blog, we will explore the latest trends in enterprise cybersecurity and discuss how your organization can navigate the complex enterprise cybersecurity landscape.

Enterprise Cybersecurity Trends: A Changing Landscape
The cybersecurity landscape is constantly evolving, driven by advancements in technology and the increasing prevalence of cyber threats. To effectively protect your business, it is essential to understand and embrace the following key trends:
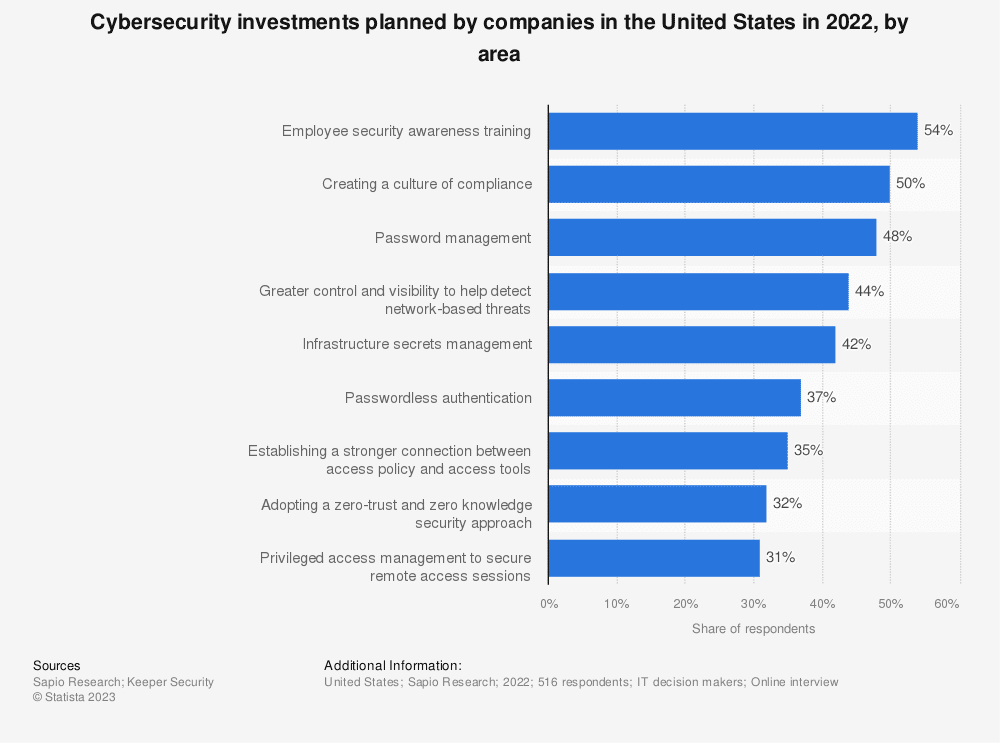
1. Employee Cybersecurity Training
Human error remains one of the leading causes of cyber incidents. With so many cybersecurity threats circulating, investing in comprehensive employee cybersecurity training is crucial to create a security-conscious culture within your organization. According to a report by IBM, human error is the leading cause of cyber incidents By educating employees about common cyber threats, promoting best practices, and conducting regular awareness programs, you can empower your workforce to be the first line of defense against cyber attacks.
2. Shift to Zero Trust Security Model
In 2009, Forrester analyst John Kindervag predicted the rapid approach of this shift and introduced the concept of zero trust. The traditional perimeter-based security approach is no longer sufficient in today’s dynamic threat landscape. The Zero Trust security model has gained prominence, focusing on strict access controls and authentication for every user and device, regardless of their location or network. By adopting a Zero Trust approach, enterprises can minimize the risk of unauthorized access and mitigate the impact of potential breaches.
3. Cloud Security
With the widespread adoption of cloud services, organizations must prioritize robust cloud security measures. Securing cloud environments, data storage, and cloud-native applications is critical as data moves beyond traditional network boundaries. Implementing strong encryption, multi-factor authentication, and continuous monitoring can help fortify cloud-based assets against cyber threats.
4. Artificial Intelligence (AI) in Cybersecurity
As cyber threats become more sophisticated, organizations are turning to AI-powered solutions to enhance their cybersecurity capabilities. AI can analyze vast amounts of data, detect anomalies, and identify patterns indicative of potential threats in real-time. Enterprises can strengthen their threat detection and response capabilities by leveraging AI-driven tools like behavioral analytics and machine learning algorithms.
5. Internet of Things (IoT) Security
The surge of IoT devices brings new security challenges for enterprises. From connected devices in offices to industrial control systems, securing the IoT ecosystem is critical to prevent unauthorized access and potential disruption. Implementing robust authentication mechanisms, regular patching, and network segmentation can help mitigate IoT-related security risks.
Looking Beyond the Enterprise Cybersecurity Trends
To safeguard your business in the digital age, addressing these emerging cybersecurity trends is essential.
Here are some steps your organization can take:
- Assess Your Security Posture: Conduct a thorough assessment of your current security infrastructure, policies, and procedures. Identify any vulnerabilities or gaps that need to be addressed to align with the latest trends.
- Implement a Zero Trust Framework: Move away from a perimeter-based security model and adopt a Zero Trust approach. Implement strong access controls, multi-factor authentication, and continuous monitoring to ensure the highest level of security for your digital assets.
- Enhance Cloud Security: Implement robust cloud security measures to protect your data and applications in the cloud. Utilize encryption, access controls, and regular vulnerability assessments to mitigate risks associated with cloud-based environments.
- Leverage AI-driven Solutions: Explore AI-powered tools and solutions that can augment your cybersecurity capabilities. Implement behavioral analytics, machine learning algorithms, and threat intelligence platforms to effectively detect and respond to threats.
- Prioritize IoT Security: Develop a comprehensive IoT security strategy that includes device authentication, regular patching, and
Use Olive to Source Your Security Tech Stack and Focus on Your Needs
Stop Focusing on Enterprise Cybersecurity Trends; Start Focusing on Your Needs
In the complex world of enterprise cybersecurity, it’s important to prioritize your specific requirements. Olive helps you identify your needs and streamline the vendor selection process. By entering your requirements into Olive’s platform, you can invite multiple vendors to respond and align their solutions with your needs. Incorporate insights from other stakeholders and ensure integration and implementation requirements are met. Continuously monitor and assess your security posture with Olive’s platform. Let Olive guide you in sourcing your security tech stack and protecting your business effectively.